Have you ever heard about keyloggers?. Just in case you haven’t… keyloggers are a super simple piece of technology. They are software applications that can be installed in almost every PC / Mac, and they simply save every keystroke.
They’re invisible to the user. So… they just know everything you type. Including passwords. Keyloggers generate a logfile, which can be (in some cases) sent via email to the guy who is spying on you… and in other cases, they just generate a textfile somewhere in the system… which will eventually be downloaded, and your whole security exposed.
So… long short story, keyloggers are a threat to your email account, homebanking, skype, facebook… everything you use online, can be super easily “hacked”. That includes Dropbox!.
I don’t know about you, but i store personal files in Dropbox, such as pictures, and documents… i just use it as an online backup “just in case”. If i got hacked, the idea of someone else skimming through my stuff… well, it’s pretty scary.
So, what can we do?
Let’s set up Two Step Authentication!
- First things first. We’re gonna need to install Google Authenticator app. So, if you use an iOS device, get it here. If you’re an android user… (shame on you!)… get it here.
- Head to dropbox.com, and login with your account.
- Click in the top right corner, and find the ‘Settings’ link.
- Click on the ‘Security’ tab. You should see the following:
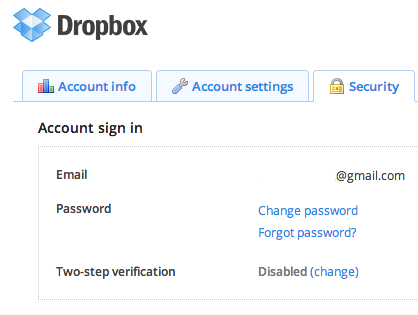
- See the ‘Two-step verification’ option?. Click on ‘Change!’
- Follow the instructions, until you get the following barcode onscreen:
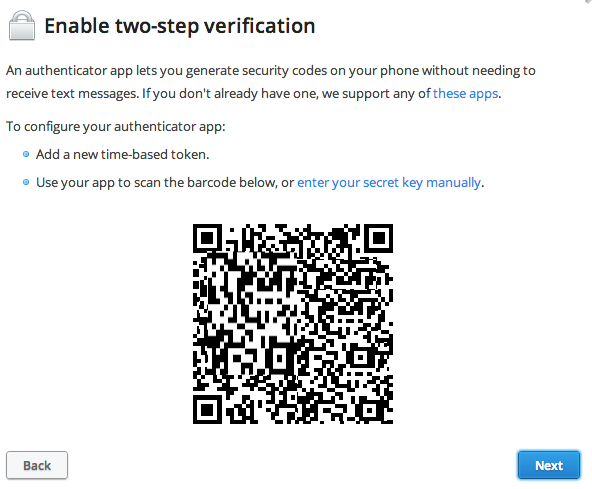
- Well, at this point, you need to launch Google Authenticator App. Tap the ‘ + ‘ button, and tap the ‘Scan Barcode’ option. You’re gonna need to scan the QR code you’ve got onscreen.
- If everything went fine, your Google Authenticator app should already have an entry with a 6 digit number matching your Dropbox Account.
- Please, keep somewhere safe your 6 digit rescue code. That will save you, in case of emergency.
- You’re all set!.
Next time you log into your Dropbox account, the system will ask you to enter the 6 digits given by Google Authenticator app. Why is it good? why you should use it?….
Remember when we spoke about keyloggers?. Well, imagine you’ve got a keylogger installed in your computer….. no one, even with your passwords, will be able to log into your account. Unless they ALSO have your phone.
It’s an extra security measure, which makes things even more complicated. You’re not unhackable. But at least no script kiddie will be able to simply hijack your system.
Stay safe!


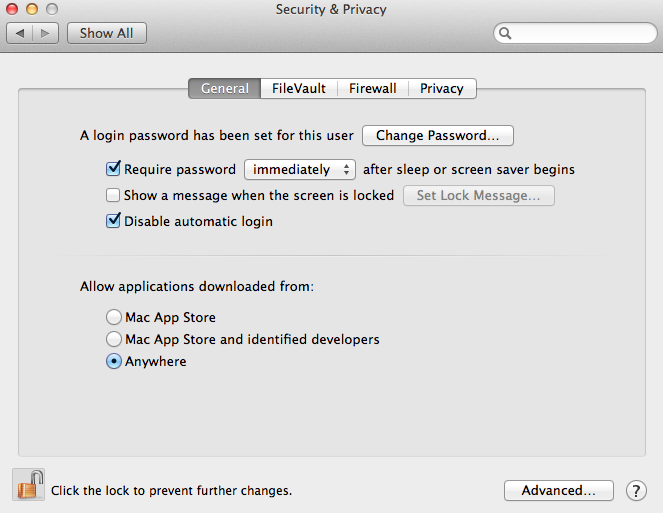
 So… you own an iMac.. maybe a Macbook Pro, or maybe you’re one of the lucky owners of a Mac Pro. You’ve been watching ads for the last ten years… you bought it all, and you feel safe just because it’s not a windows… right?.
So… you own an iMac.. maybe a Macbook Pro, or maybe you’re one of the lucky owners of a Mac Pro. You’ve been watching ads for the last ten years… you bought it all, and you feel safe just because it’s not a windows… right?.